Cybersecurity
-

The secret to successful exit: Software audit
Have you ever thought about the legal implications of excessive use of NPM? Project A’s Tech team shares some insights gleaned from numerous due diligence processes and offers best practices for working with open-source and third-party libraries
-

Say goodbye to dependency hell, supply chain attacks, and performance issues
Package managers are lifesavers — until a dubious developer decides to inject malicious code into their open-source library. Tips, resources, and best practices that will help you build safer, more stable, and performant apps
-

Are you a data exhibitionist? why you should protect your sensitive ports
You rarely set out to be a data exhibitionist. It happens surreptitiously. Then one day, your databases end up on Shodan, naked and exposed
-
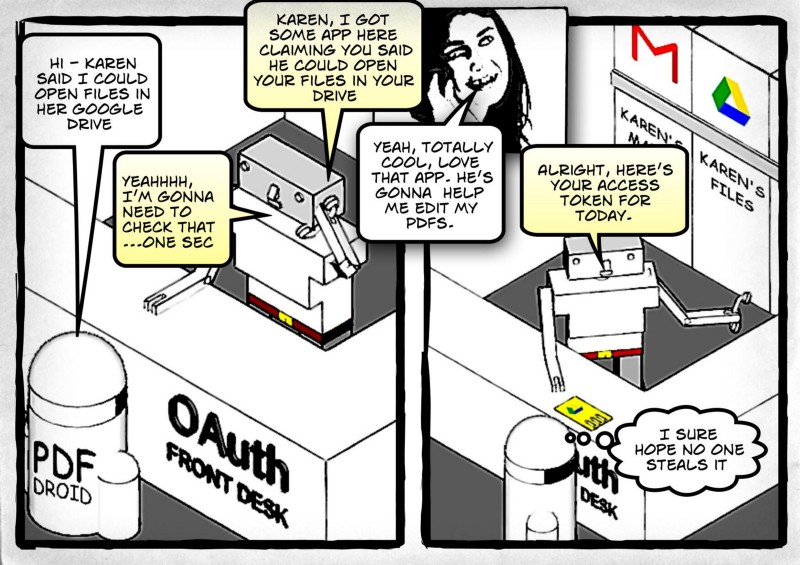
Do you monitor how third-party apps use your SaaS accounts? You should
Third-party apps can have more access privileges than you would expect. But should you prevent employees from installing apps themselves?
-
How to Take Your WiFi Security to the Next Level — with RADIUS
Simple WiFi passwords represent a security vulnerability—what can you do to protect yourself?
-

Signing GitHub Commits with a GPG Key
Why you should sign your GitHub Commits with a GPG Key and how to set it up